Data Governance - Security and Compliance Metrics
Understanding where data comes from, how it is transformed, and where it moves over time is vital for both compliance and data quality. This includes detailed histories of data sources, transformations applied, and downstream uses.Understanding where data comes from, how it is transformed, and where it moves over time is vital for both compliance and data quality. This includes detailed histories of data sources, transformations applied, and downstream uses.
Security and Compliance Metrics are essential components of a Data Governance Platform, serving as critical indicators of an organization's adherence to security standards and regulatory compliance. These metrics provide a comprehensive view of the security posture and compliance status of data across an organization, helping to identify vulnerabilities, monitor for compliance with legal and policy requirements, and ensure that data protection measures are effective.
1. Access Controls and Audit Logs: Security and compliance metrics track who is accessing data, when, and for what purpose. Audit logs are maintained to record all access and modification events related to sensitive data. These logs are crucial for forensic analysis in the event of a security incident and for regular compliance audits. Access controls ensure that only authorized personnel can access sensitive data based on their role and responsibilities.
At the Data Object Layer, ARPIA leverages MySQL binary logs (binlogs) for transaction-level auditing and supports point-in-time recovery at the database level. Separately, all changes to Knowledge Grid (KG) Nodes are recorded in the platform audit log, allowing administrators to review and revert Node-level changes to any prior state.
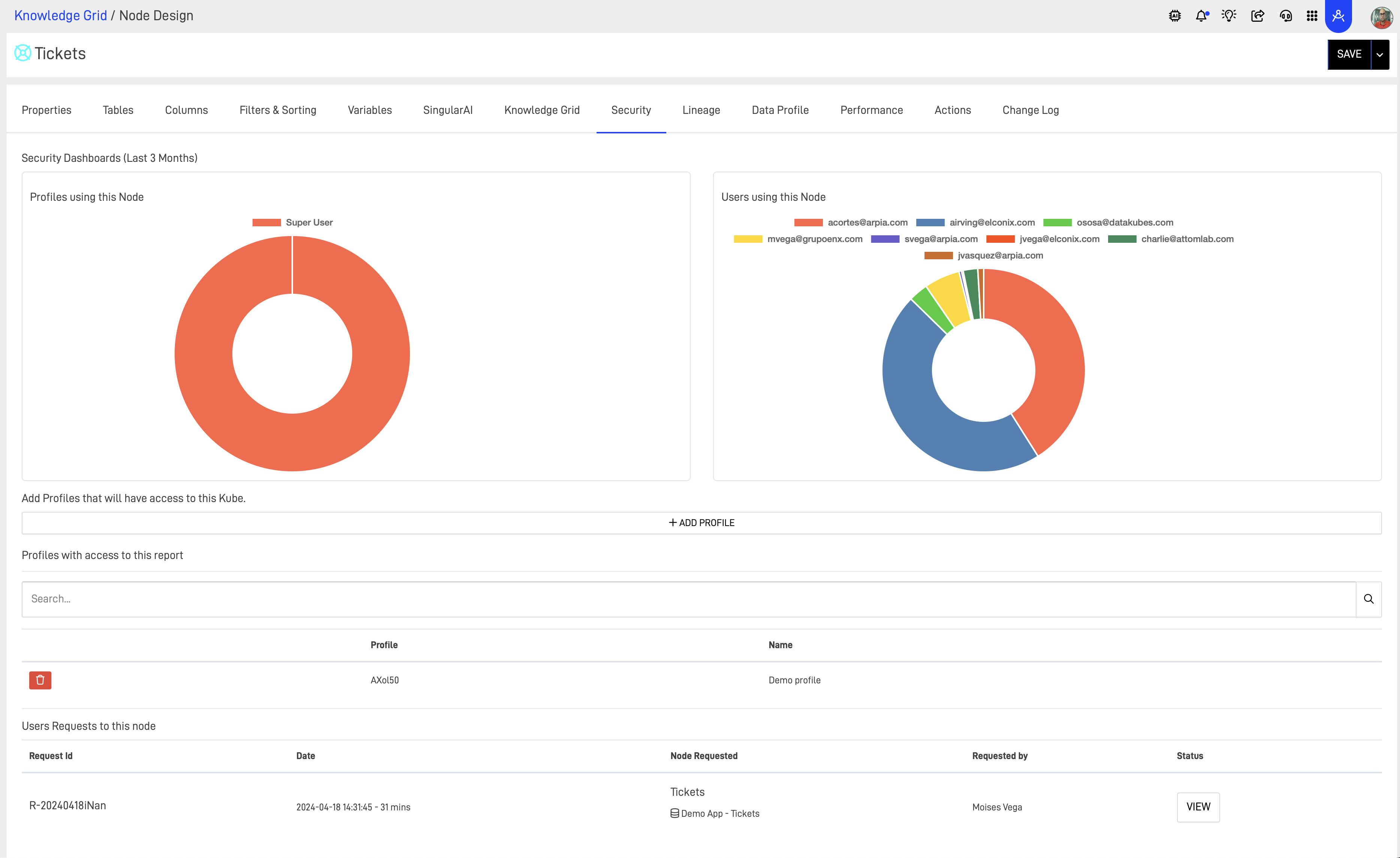
User & Profile management in ARPIA.
2. Data Encryption Metrics: Metrics related to data encryption help ensure that data at rest and in transit is protected according to best practices. This includes monitoring the strength of encryption methods, the management of encryption keys, and compliance with industry standards such as PCI-DSS for payment data or HIPAA for health information. In ARPIA, encryption at rest is configurable at the time of Repository setup, and is available at both the OS and Data Repository levels. All data in transit is transmitted over encrypted connections.
3. Vulnerability Assessments and Penetration Testing: Security metrics include results from regular vulnerability assessments and penetration tests. These tests identify and remediate security vulnerabilities across the platform's infrastructure, including databases, applications, and network systems. Results are used to prioritize security issues based on severity and potential impact. Penetration test results and related security documentation are available to customers and prospective customers upon request.
4. Incident Response Metrics: These metrics track the organization's ability to detect, respond to, and recover from security incidents. Key performance indicators include Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR). ARPIA maintains internal incident response processes aligned with these KPIs. Additionally, organizations can leverage the ARPIA Data Platform to build custom incident management applications and generate analytics dashboards to support their own incident tracking and reporting workflows.
5. Data Breach Metrics: In the event of a data breach, these metrics detail the scope, impact, and nature of the incident — including the types of data compromised, the number of individuals affected, and the status of containment and mitigation efforts. These metrics support regulatory reporting obligations and inform ongoing improvements to data security measures. ARPIA maintains internal breach response procedures, and organizations can also use the Data Platform to build custom breach tracking and reporting applications.
6. User Behavior Analytics: By monitoring and analyzing user behavior, security teams can identify anomalies that may indicate a security threat, such as unauthorized access attempts or data exfiltration. In ARPIA, every KG Node maintains a detailed access log that records how data is delivered and consumed across the platform, enabling administrators to detect and respond to unauthorized access patterns.
By continuously monitoring these metrics, organizations can effectively manage security risk, maintain compliance with applicable regulatory requirements, and build trust with customers, regulators, and partners.
Updated 2 months ago
